Plesk Obsidian 18.0.77 Is Here: Significant Accessibility Developments and New ACME SSL Support
We are excited to announce the latest release of Plesk Obsidian: v18.0.77. This update brings one…

We are excited to announce the latest release of Plesk Obsidian: v18.0.77. This update brings one…

Introduction: Allowing excessive login attempts on cPanel exposes your server to brute force attacks that can…

How to Stop Unauthorized Server Spam To Stop Server Outbound Spam, engineers must identify compromised scripts,…
High bandwidth connections do not automatically guarantee fast data transfers across continents. Many organizations discover that…

Deprecations to Note Plesk UserVoice will be sunset by October 2025. Feature requests are now managed…
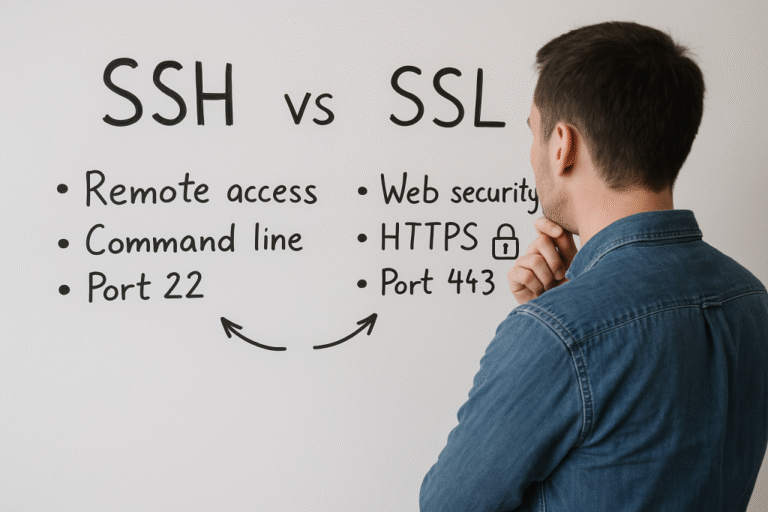
Understanding SSH Definition and Purpose SSH stands for Secure Shell. It is a cryptographic network protocol…
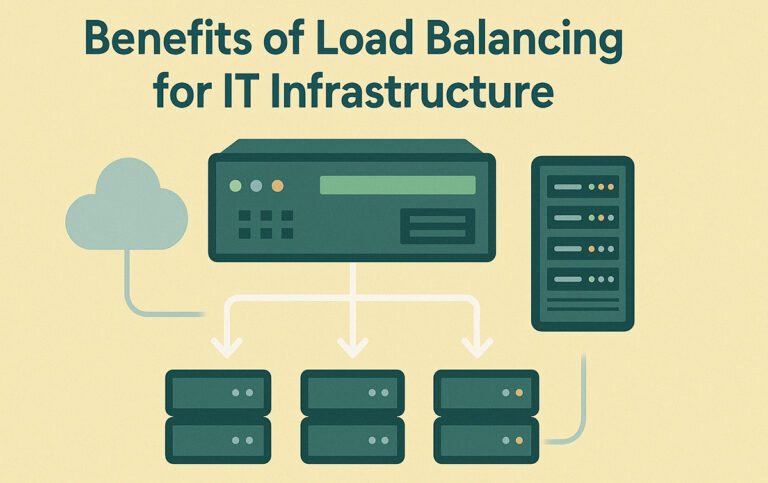
In the contemporary digital landscape, the expectation for uninterrupted service and seamless scalability is paramount. At…

Table of Contents Get started today!◦ Full contract buyout ◦ Up to $1,000 credit ◦ Free…
Table of Contents Get started today!◦ Full contract buyout ◦ Up to $1,000 credit ◦ Free…