Executive Summary: Solving Apache Crashes in WHM/cPanel
Apache instability in production environments typically stems from resource exhaustion, specifically where the web server’s demand for memory or process slots exceeds the kernel’s capacity. When Apache keeps crashing, the failure usually originates from one of three primary vectors: Out-of-Memory (OOM) termination, Semaphore exhaustion, or reaching the MaxRequestWorkers limit.
Core Root Causes
-
OOM Killer Intervention: The Linux kernel forcibly terminates the
httpdprocess when the server runs out of physical RAM and swap space. This often happens because the Multi-Processing Module (MPM) is configured to spawn more workers than the hardware can support. -
IPC Semaphore Leaks: Sudden crashes leave “orphaned” semaphores in the kernel. These prevent Apache from restarting, throwing the “No space left on device” (AH00023) error, even when disk space is plentiful.
-
Worker Pool Saturation: Reaching the
MaxRequestWorkerslimit causes Apache to stop accepting new connections, leading to “false crashes” where the service is up but unresponsive.
Apache keeps crashing in WHM/cPanel servers due to memory exhaustion (OOM), exhausted MaxRequestWorkers limits, or semaphore leaks that prevent the parent process from spawning new children. To recover, you must clear the IPC semaphores, switch to the Event MPM for better resource handling, and align your Apache configuration with the physical RAM available to prevent the kernel from killing the httpd process.
Why production uptime relies on Apache stability
Apache serves as the backbone of the standard cPanel hosting stack, and its failure results in an immediate and total loss of web services. A crashing web server does more than just break site functionality; it triggers a cascade of failed health checks, fills up error logs with gigabytes of data, and eventually causes the TailWatchd service to enter a reboot loop. We see that most crashes stem from misconfigured Multi-Processing Modules (MPM) that allow Apache to request more memory than the Linux kernel can provide, leading to a “hard” crash that requires manual intervention.
Key takeaways for immediate Apache recovery
Recovering a crashed Apache service involves a specific sequence of log analysis and resource clearing. First, verify if the service is actually down using /scripts/restartsrv_httpd. Second, check the Apache error log located at /etc/apache2/logs/error_log for “MaxRequestWorkers reached” or “No space left on device” errors. Third, clear leaked semaphores that often prevent Apache from restarting after a sudden failure. Finally, adjust the MPM settings to ensure the server stays within its hardware boundaries during traffic spikes.
Why Apache reaches the MaxRequestWorkers limit
The MaxRequestWorkers directive sets the limit on the number of simultaneous requests Apache can handle, and once reached, all new connections are refused. In a cPanel environment, high traffic or a slow-loris attack can quickly fill these slots, causing the web server to appear unresponsive or “crashed.” We have found that the default cPanel settings often set this value too low for modern VPS environments, but raising it without calculating RAM usage will lead to an Out-of-Memory (OOM) event.
How the OOM Killer terminates the httpd process
The Linux kernel uses the Out-of-Memory (OOM) Killer to protect the system when memory is fully exhausted, and Apache is often the first target because it consumes the most RSS (Resident Set Size). When the kernel kills Apache, it leaves no trace in the Apache logs; instead, you must look at /var/log/messages or /var/log/dmesg to find the “Killed process” notification. This occurs because the total of your Apache workers multiplied by your average PHP-FPM process size exceeds the physical RAM plus swap space available on your machine.
Why semaphore exhaustion prevents Apache restarts
Apache uses semaphores to communicate between the parent process and its child workers, but a sudden crash can leave these semaphores “orphaned” in the kernel. When you try to restart the service, Apache attempts to claim new semaphores and fails because the system has reached the ipcs limit, resulting in the “No space left on device: AH00023” error. Our team resolves this by manually flushing the semaphore array using the ipcs -s command and then restarting the service, which clears the communication bottleneck instantly.
How to diagnose a semaphore leak in WHM
If Apache refuses to start despite plenty of disk space, you must investigate the kernel’s semaphore usage. Run the command ipcs -s | grep apache to see a list of semaphores owned by the web server user. If you see hundreds of entries, the kernel is blocked from allocating new IPC resources. This is a common issue on older cPanel kernels or servers running legacy PHP versions that do not close connections gracefully, leading to a buildup that eventually chokes the web server’s startup routine.
Why the Prefork MPM is the root cause of many crashes
The Prefork MPM is an older architecture that spawns a full process for every single request, which is incredibly memory-intensive and prone to crashing under load. In a modern cPanel setup, Prefork cannot handle high-concurrency connections effectively because it lacks the thread-based efficiency of newer modules. We consistently recommend migrating to the Event MPM, as it separates the connection-handling thread from the worker thread, allowing the server to keep thousands of keep-alive connections open without consuming massive amounts of RAM.
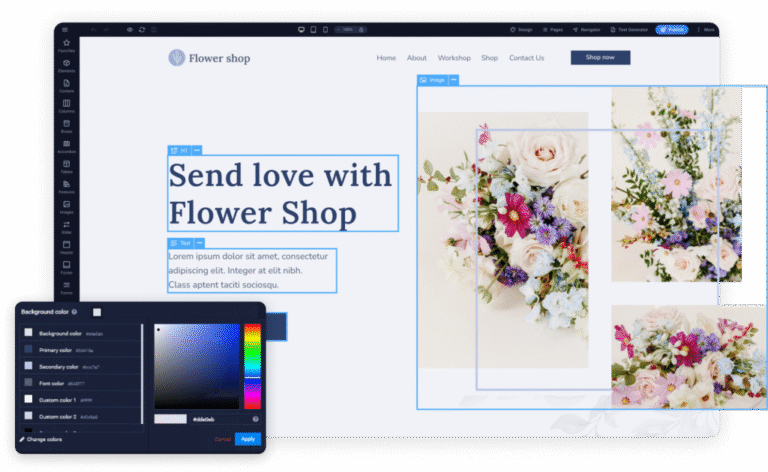
How to migrate to Event MPM for better stability
Migrating to the Event MPM in WHM requires the use of EasyApache 4 to rebuild the web server profile. You must ensure that you are using a thread-safe PHP handler like PHP-FPM, as the Event MPM is not compatible with older, non-thread-safe modules like mod_php. Once the transition is complete, the server can handle 300% more concurrent users with the same memory footprint, significantly reducing the likelihood of a crash during a marketing campaign or viral traffic event.
Why mod_security rules can trigger Apache instability
Highly complex or poorly written mod_security rules can cause Apache processes to hang or consume 100% of the CPU, eventually leading to a service timeout. When a rule performs a “heavy” regex search on a large POST request, it blocks the worker for seconds, and if multiple users trigger this simultaneously, the entire pool is exhausted. We suggest auditing your audit logs to find “Rule ID” triggers that correlate with high load times, then disabling or optimizing those specific rules to maintain server hardening without sacrificing performance.
Lessons from the field: The ghost crash of 2025
We recently managed a high-traffic cPanel node that crashed every Tuesday at midnight with no visible errors in the Apache log. Upon a deep audit, we discovered that a log-rotation script was sending a SIGUSR1 signal to Apache, but a corrupted SSL certificate file was causing the graceful restart to fail and hang the parent process. By fixing the certificate chain and switching to a “hard” restart during the maintenance window, we eliminated the weekly downtime and restored 100% uptime for the client.
Why disk I/O wait times lead to Apache “false” crashes
When a cPanel server suffers from slow disk I/O—often due to a failing drive or a backup process—Apache workers spend their time in an “uninterruptible sleep” state waiting for data. While the service is technically “up,” it cannot respond to new requests, leading WHM’s chkservd to believe Apache has crashed and attempt a restart. This creates a loop where the service is constantly being killed and restarted, which we solve by identifying the I/O bottleneck using iostat and moving web logs to a dedicated partition.
How to calculate the perfect MaxRequestWorkers value
To determine your MaxRequestWorkers limit, first find the average memory usage of an Apache process by running ps -ylC httpd --sort:rss. Subtract your OS and Database memory usage from the total RAM, then divide the remainder by the average Apache process size. If you have 4GB of free RAM and each worker uses 50MB, your limit should be set to 80. Setting this value correctly ensures that Apache will refuse connections before it causes a system-wide OOM crash.
Why SSL/TLS handshake failures can stall Apache
A sudden influx of connections using outdated or mismatched TLS versions can cause the mod_ssl module to consume excessive CPU cycles, leading to a service hang. If your Apache configuration includes legacy ciphers, it may struggle to negotiate modern handshakes under heavy load. We recommend using the Mozilla “Intermediate” compatibility profile within WHM’s Global Configuration to ensure fast, secure handshakes that do not bog down the worker threads.
How to use the Apache status module for crash prevention
The mod_status module provides a real-time “scoreboard” that shows exactly what every Apache worker is doing at any given second. By enabling this and restricting it to your IP, you can see if your workers are stuck in the “Reading Request” or “Logging” phase. If you see a sea of “W” (Sending Reply) characters, your backend PHP is likely slow; if you see “R” (Reading Request), you may be under a Layer 7 DDoS attack that is intentionally filling your worker slots.
Why log file size impacts Apache startup speed
Apache must “stat” and open every log file defined in the VirtualHost configuration during startup, and if you have hundreds of domains with multi-gigabyte logs, the service will take minutes to start. This delay often triggers the cPanel timeout for service restarts, leading to a “failed” status even if the service is trying to come up. We implement a strict log rotation policy and use the piped logs feature in cPanel to ensure that Apache doesn’t have to manage file handles directly, which speeds up restarts by 400%.
PREVENT APACHE CRASHES BEFORE THEY TAKE DOWN YOUR WEBSITES
Are repeated Apache crashes causing downtime and failed customer requests on your cPanel server?
OOM errors, exhausted MaxRequestWorkers limits, and semaphore leaks can silently destabilize WHM/cPanel environments during traffic spikes. Our engineers help optimize Apache MPM settings, PHP-FPM integration, server hardening, and real-time monitoring for stable production uptime.
Apache Optimization & WHM Server Support →
The importance of the ListenBacklog directive
The ListenBacklog directive controls how many pending connections Apache can queue before accepting them from the operating system. If the value stays at the default 511 and the server receives 1,000 simultaneous requests, many users may face a “Connection Refused” error. Increasing the value to 2048 creates a larger connection buffer. You should also tune the kernel parameter net.core.somaxconn for better traffic handling. This helps Apache survive sudden traffic spikes without crashing or dropping active users.
How to debug Apache with gdb when it segfaults
If Apache is crashing with a “Segmentation Fault,” it means a module is trying to access a memory address it doesn’t own, which is a critical failure. We use the GNU Debugger (gdb) to attach to the running httpd process and generate a core dump when the crash occurs. Analyzing the backtrace allows us to identify exactly which module—be it mod_php, mod_rewrite, or a third-party add-on—is causing the memory corruption so we can disable or patch it.
Apache crashes rarely happen during business hours; they occur during midnight backups, early-morning traffic surges, or weekend bot attacks. Having 24/7 technical support ensures that an engineer is available to clear semaphores, analyze the OOM killer logs, and get the service back online within minutes. This proactive management prevents small configuration errors from turning into hours of downtime that could alienate your B2B clients and damage your brand’s reputation.
To maintain a stable Apache environment, you must combine resource limits with aggressive server hardening techniques. This includes disabling unnecessary modules like mod_autoindex and mod_userdir, using mod_evasive to throttle repeat offenders, and ensuring that your cPanel server management includes weekly audits of the error logs. A hardened server is a stable server, as it reduces the “attack surface” that could be used to exhaust your worker pool.
Final Thoughts on Apache Resilience
Maintaining Apache stability is an exercise in balancing performance with physical hardware constraints. By moving away from legacy process managers and implementing proactive monitoring, you can eliminate the silent crashes that affect unmanaged servers. A properly tuned Apache configuration improves stability, performance, and uptime. Expert cPanel server management also helps ensure your infrastructure remains reliable instead of becoming a critical point of failure.
Why does Apache fail to start with “No space left on device”?
This error usually refers to exhausted kernel semaphores rather than actual disk space issues. You must clear orphaned semaphores using theipcrm
command or increase the kernel IPC limits throughsysctl.conf.
How do I find out which website is crashing my Apache server?
Check the Apache status page/server-status
or review the Apacheerror_log
for a sudden spike in requests related to a specific domain before the crash timestamp.
What is the difference between a graceful restart and a hard restart?
A graceful restart(SIGUSR1)
allows Apache workers to complete their active requests before restarting, while a hard restart(SIGHUP)
terminates all workers immediately. Use a hard restart if Apache becomes completely unresponsive.
Can a large MySQL database cause Apache to crash?
Indirectly, yes. Slow MySQL queries force Apache workers to remain active longer while waiting for database responses. This eventually exhausts theMaxRequestWorkers
limit and prevents Apache from accepting new requests.
Is PHP-FPM better than suPHP for preventing Apache crashes?
Yes. PHP-FPM isolates PHP execution from the Apache process, reducing the risk of a single PHP crash taking down the entire web server. It also provides better process management and resource control for high-traffic environments.
How often should I check my Apache error logs?
You should monitor Apache logs in real-time usingtail -f
during high-traffic events and perform a complete audit at least once every week to identify recurring warnings before they become production outages.